HoT-TAI-0002: Injection
HoT-TAI-0002: Injection
Summary:
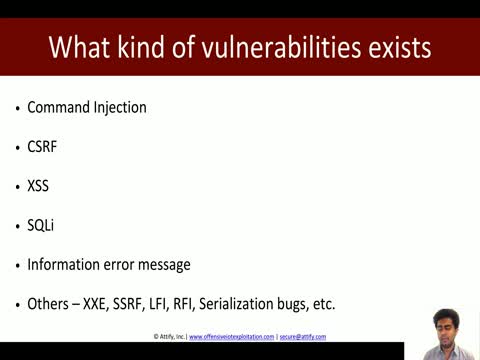
- CWE-74 Injection: Improper neutralization of special elements in output used by a downstream component, or in layman terms "injection" is a vulnerability in which the software constructs all or part of a command, data structure, or record using externally-influenced input from an upstream component, but it does not neutralize or incorrectly neutralizes special elements that could modify how it is parsed or interpreted when it is sent to a downstream component. Software has certain assumptions about what constitutes data and control respectively. It is the lack of verification of these assumptions for user-controlled input that leads to injection problems. Injection problems encompass a wide variety of issues -- all mitigated in very different ways and usually attempted in order to alter the control flow of the process. For this reason, the most effective way to discuss these weaknesses is to note the distinct features which classify them as injection weaknesses. The most important issue to note is that all injection problems share one thing in common -- i.e., they allow for the injection of control plane data into the user-controlled data plane. This means that the execution of the process may be altered by sending code in through legitimate data channels, using no other mechanism. While buffer overflows, and many other flaws, involve the use of some further issue to gain execution, injection problems need only for the data to be parsed. The most classic instantiations of this category of weakness are SQL injection and format string vulnerabilities.1 See also:
- CWE-75 Special element injection
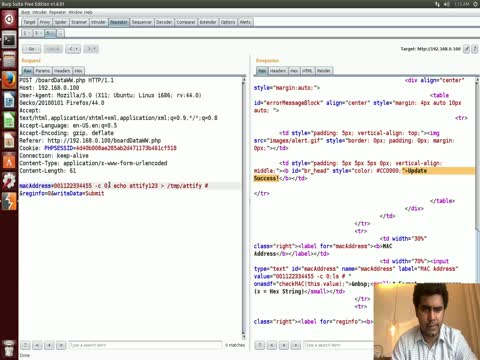
- CWE-77 Command injection
- CWE-79 Cross-site scripting
- CWE-89 SQL Injection
- CWE-91 XML / Blind XPath injection
- CWE-93 CRLF injection
- CWE-94 Code injection
- CWE-99 Resource injection
- CWE-134 Use of externally-controlled format string
- CWE-138 Improper neutralization of special elements
- CWE-943 Improper neutralization of special elements in data query logic
Estimated Overall Risk Assessment: HIGH
Technical Impacts:
HIGH- Injection attacks allow attackers to "read application data", "bypass protection mechanisms", "alter execution logic", violate data integrity, and hide activities.
Business Impacts:
HIGH- Data confidentiality, integrity, and availability could be compromised. An attacker could gain control over the IoT device and could establish a foothold within your network for further actions-on-objective (e.g. further exploitation of internal network OR to utilize the IoT device as part of a botnet to launch attacks against national critical infrastructure).
Detectability:
Dependent upon language and implementation (e.g. known SQLi attacks can be EASILY detected with tools such as sqlmap or w3af, if implemented through a web application)Prevalence:
COMMONExploitability:
EASY
Attack Surfaces Grouped By Layer of Cyberspace
- Physical Network Layer
- Device Network Services
- Device Web Interface (OWASP Web Top10)
- Logical Network Layer
- Vendor Backend APIs
- Cloud Web Interface (OWASP Web Top 10)
Known Intrusion / Exploit / Attack Cases and Threats
- TheMoon
- Description: Exploits a vulnerable CGI script (command injection?); Target: Linksys routers2
- Amnesia Botnet
- Description: Exploits an unpatched remote code execution vulnerability (injection or buffer overflow?); Subsequent bot is utilized to conduct DDoS attacks; Employs VM detection and evasion techniques to prevent malware analysis. Target: CCTV-DVR made by TVT (to get closer to PoS systems).3
- Persirai Botnet
- Description: Exploits a command injection vulnerability; (can also uses additional exploits); Subsequent bot is utilized to conduct DDoS attacks; Target: IP cameras4
- Imeij Botnet
- Description: Exploits an authenticated command injection vulnerability; Subsequent bot conducts reconnaissance, executes local shell commands, conducts DDoS attacks, and terminates itself. Target: Linux internet connected devices produced by AVTech.5
- Linux.Darlloz
- Description: A worm that exploits a php-cgi vulnerability (CVE-2012-1823;input validation/injection). Subsequently conducts a DoS on the local device by deleting files and dropping packets destined to certain ports (e.g. Telnet); a backdoor is then created which waits for commands.Target: Routers, IP cameras, DVR/set-top boxes and other vulnerable IoT devices.6
Identify, Detect, Protect, Respond, and Recover (NIST FICIC)
This vulnerability page (and some information contained in the associated attack page) address the following:
IDENTIFY-RISK ASSESSMENT (ID.RA)
- ID.RA-1: Asset vulnerabilities are identified and documented
- See "Analysis Tools and Training" below.
- ID.RA-2: Cyber threat intelligence and vulnerability information is received from information sharing forums and sources
- ID.RA-3: Threats, both internal and external are identified and documented
- ID.RA-4: Potential business impacts and likelihoods are identified
- ID.RA-5: Threats, vulnerabilities, likelihoods, and impacts are used to determine risk
- IS.RA-6: Risk responses are identified and prioritized
- ID.RA-1: Asset vulnerabilities are identified and documented
PROTECT-Information Protection Processes and Procedures (PR.IP)
- PR.IP-12: A vulnerability management plan is developed and implemented
DETECT-Anomalies and Events (DE.AE)
- DE.AE-2: Detected events are analyzed to understand attack targets and methods
DETECT-Security Continuous Monitoring (DE.CM)
- DE.CM-1: The network is monitored to detect potential cybersecurity events
Analysis Tools and Training
Identify
Online attacks (Device Network Services, Web, and Cloud)
Using tools such as w3af, arachni, or nikto to identify known SQLi, command injection, etc. vulnerabilities.
Using sqlmap to identify and exploit DBMS (MySQL, Oracle, PostgreSQL, MS-SQL, Microsoft Access, IBM DB2, SQLite, Firebird, Sybase, SAP MaxDB, HSQLDB and Infromix) that are vulnerable to (6) types of SQLi (boolean-based blind, time-based blind, error-based, UNION query-based, stacked queries, and out-of-band). In addition, sqlmap has a ton of useful exploitation and post exploitation features. It is also possible to connect directly to the DB without a SQLi if you have the DBMS credentials, IP address, port and database name.
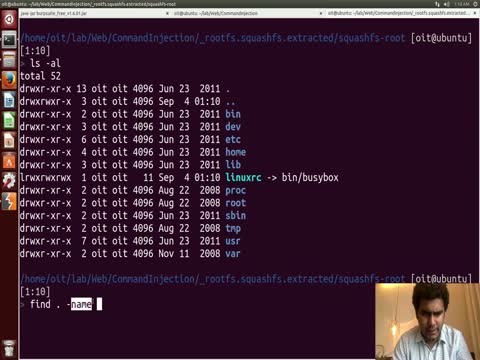
Offline attacks
- Firmware analysis to identify SQLi, command injection, etc. vulnerabilities.
Associated CVEs / Manufacturers / Devices
Use this link to identify the latest injection vulnerabilities. This search query is not specific to the IoT.
Use this link to identify the latest command injection vulnerabilities. This search query is not specific to the IoT.
Use this link to identify the latest XSS vulnerabilities. This search query is not specific to the IoT.
Use this link to identify the latest SQL injection vulnerabilities. This search query is not specific to the IoT.
Use this link to identify the latest XML injection vulnerabilities. This search query is not specific to the IoT.
Use this link to identify the latest XRLF injection vulnerabilities. This search query is not specific to the IoT.
Use this link to identify the latest code injection vulnerabilities. This search query is not specific to the IoT.
Use this link to identify the latest resource injection vulnerabilities. This search query is not specific to the IoT.
Use this link to identify the latest format string vulnerabilities. This search query is not specific to the IoT.
Use this link to identify the latest improper neutralization of special elements in data query logic vulnerabilities. This search query is not specific to the IoT.
References
- http://cwe.mitre.org/data/definitions/74.html
- https://www.cyber.nj.gov/threat-profiles/botnet-variants/themoon
- https://www.cyber.nj.gov/threat-profiles/botnet-variants/amnesia
- http://blog.trendmicro.com/trendlabs-security-intelligence/persirai-new-internet-things-iot-botnet-targets-ip-cameras/
- https://www.cyber.nj.gov/threat-profiles/botnet-variants/imeij
- https://en.wikipedia.org/wiki/Linux.Darlloz